Ssh-keygen can create RSA keys for use by SSH protocol version 1 and RSA or DSA keys for use by SSH protocol version 2. The type of key to be generated is specified with the -t option. If invoked without any arguments, ssh-keygen will generate an RSA key for use in SSH protocol 2 connections. The command ssh-keygen(1) can be used to convert an OpenSSH public key to this file format. The Diffie-Hellman Group Exchange allows clients to request more secure groups for the Diffie-Hellman key exchange. Ssh-keygen can create RSA keys for use by SSH protocol version 1 and RSA or DSA keys for use by SSH protocol version 2. The type of key to be generated is specified with the –t option. Ssh-keygen can also generate fingerprints or convert the public keys from the X.509v3 certificates specified as PKCS#11 URIs.
Use the ssh-keygen command to generate a public/private authentication key pair. Authentication keys allow a user to connect to a remote system without supplying a password. Keys must be generated for each user separately. If you generate key pairs as the root user, only the root can use the keys.
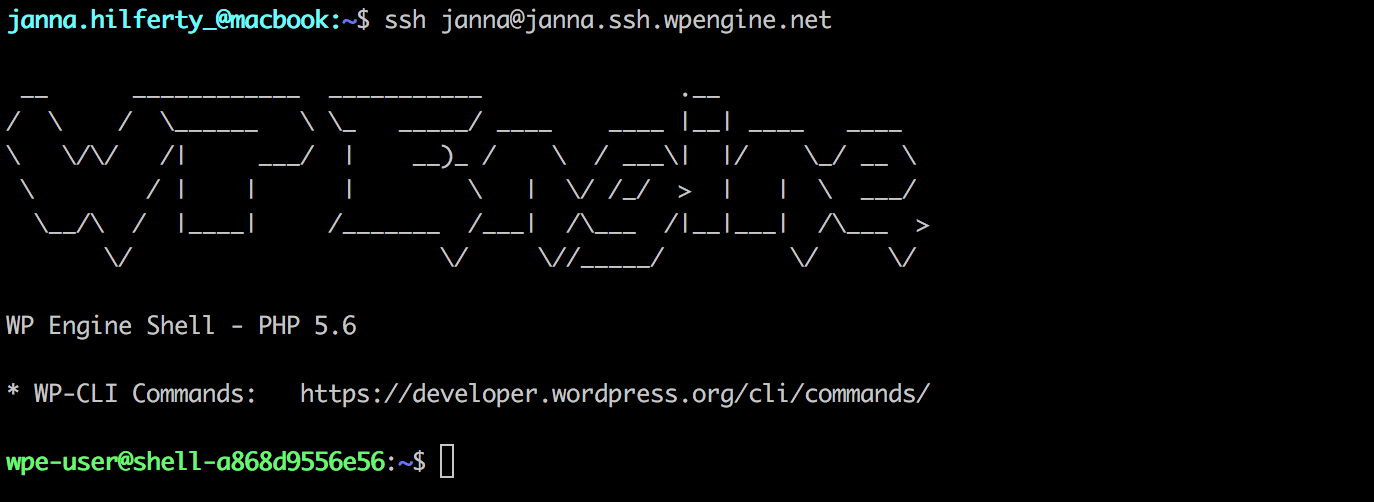
The following example creates the public and private parts of an RSA key:
Use the –t option to specify the type of key to create. Possible values are “rsa1” for protocol version 1, and “dsa“, “ecdsa“, or “rsa” for protocol version 2.
You have the option of specifying a passphrase to encrypt the private part of the key. If you encrypt your personal key, you must supply the passphrase each time you use the key. This prevents an attacker, who has access to your private key and can impersonate you and access all the computers you have access to, from being able to do so. The attacker still needs to supply the passphrase.
The ssh-key command in the example generated two keys in the ~/.ssh directory:
To log on to, or copy files to, a remote system without supplying a password, copy the public key (~/.ssh/id_rsa.pub in this example) to ~/.ssh/authorized_keys on the remote system. Set the remote ~/.ssh directory permissions to 700. You can then use the ssh or scp tools to access the remote system without supplying a password.
To allow multiple connections, append the public key to the authorized_keys file on the remote system instead of copying it. The following example appends the public key:
You can improve system security even further by disabling the standard password authentication, and enforcing the key-based authentication. To do so, set the PasswordAuthentication option to no in the /etc/ssh/sshd_config configuration file as follows:
This disallows users whose keys are not in the authorized_keys file of the specific user on the server to connect via ssh. The connection is denied and the following message appears:
Setting the PasswordAuthentication option to yes, which is the default, permits a user to use a password for authentication.
I want to check correctness of a pair of RSA key. As far as I know, I can crate a public key from a private key by using the below command, and then compare two public key if are equal or not:

ssh-keygen -y -f <PRIVATE-KEY>
The question is that, why when I use the above command, It can't load the key?
Is there any other way to check correctness of a pair of RSA keys?
FYI :
But the below command creates Proiva.der on the desktop:

This is a base64 view of my public/private files :
Private :
Public :
Note that I generate the above base64 view of my files, via this online tool.
1 Answer
It seems that your file is in DER binary format. You first need to convert the file into e.g PEM format.
To verify the file is in DER binary format run:
If it returns something like the following, then it is indeed in DER format.
Run the following:
Now your PROVIA file is converted into PEM format.
Finally run.
Valentin Bajrami
Comments are closed.